
PC Magazine Editors’ Choice Exchange Email with 99.999% SLA and J.D. Power-certified* support.
Comprehensive compliance and security capabilities including Archiving and Encryption.
Advanced email security options against ransomware, malware and phishing.
Expert migration and onboarding included free of charge.
Email is the foundation of business productivity
We offer solutions that bring added functionality to Microsoft 365 and Exchange Email to meet the unique needs of your business, whether you’re seeking to comply with GDPR or other regulations, or you’re looking to boost employee productivity with better tools. Let Intermedia help you decide which plan and combination of options is right for your business, whether you need Exchange Email, Email and Microsoft Office applications, compliance and security options, or enhanced versions of Microsoft 365. Then choose the combination of add-on services that’s right for your organisation.
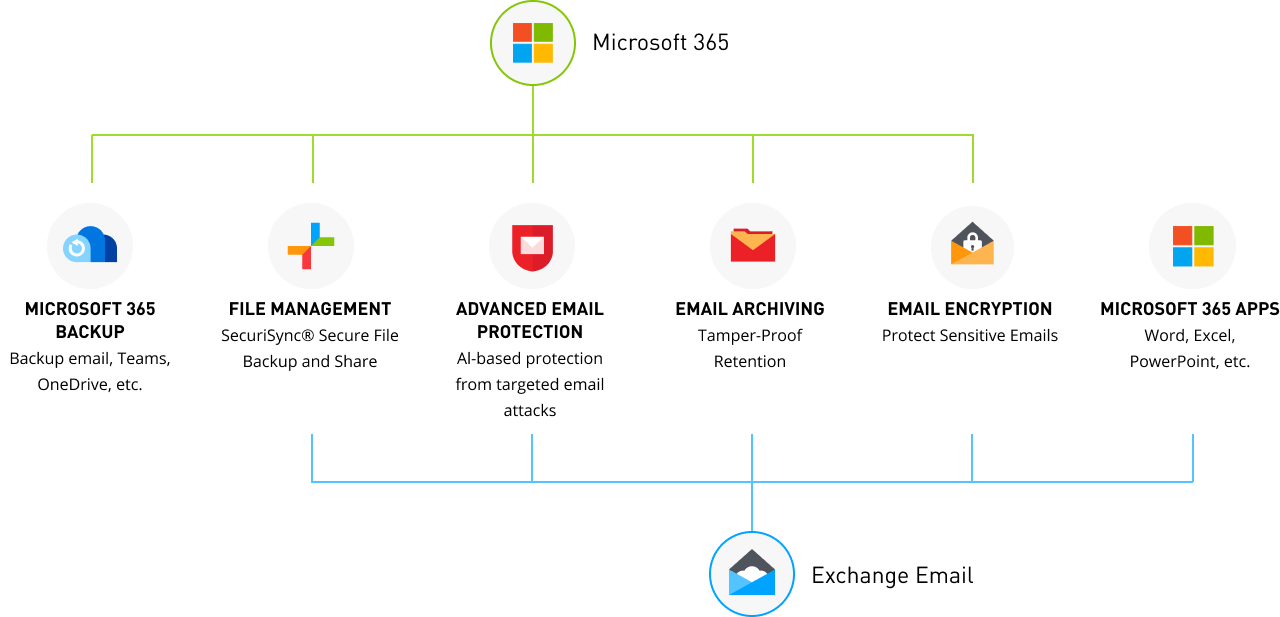
Exchange Email is only the beginning…
Exchange Business Email
from Intermedia
- Cloud-based Microsoft Exchange business email from the world’s largest independent provider
- 99.999% uptime SLA
- Unlimited email storage
- Facilitates compliance with government regulations
- Lower TCO as compared to on-premises Exchange
Protected with ADVANCED EMAIL PROTECTION
from Intermedia
- Comprehensive, multi-layered protection against malware and unknown email threats
- Anti-phishing protection against targeted email attacks
- Point-of-click protection against malicious links in emails
- Data Loss Prevention and outbound email protection
Protected with EMAIL ARCHIVING
from Intermedia
- Complete preservation of Exchange emails, including attachments
- Redundant infrastructure, data is encrypted both in transit and at rest
- Simple, flexible search and recover
- Unlimited storage and no user limit
Protected with EMAIL ENCRYPTION
from Intermedia
- Automatic encryption of Exchange emails
- Pre-built templates to help comply with regulations
- Content filtering and scanning of all outbound email
- Centralised control over email policies
Exchange Email Only
starting at£5.90/month/user
+ taxes & fees
Exchange Email + Archiving
starting at£8.00/month/user
+ taxes & fees
Why get Microsoft 365 from Intermedia?
Microsoft 365 is one of the most popular subscription-based cloud platforms available. It combines familiar Office tools with business grade email and Microsoft Teams—simplifying collaboration and enabling users to stay connected. Sold as a full suite of services, Microsoft 365 makes it easy for companies to mix and match plans to meet the needs of every employee.
Microsoft 365 from Intermedia Plans and Pricing
Build an enhanced Microsoft 365 solution with integrated Intermedia services.
Business Plans
Microsoft 365 plans for small & medium businesses (Up to 300 users) provide an integrated solution with Teams, OneDrive cloud storage, and Office apps with advanced security options—at a price that’s right for your business.
Enterprise Plans
Transform your enterprise with an integrated cloud platform that delivers industry leading productivity apps like Microsoft Teams, Word, Excel, and PowerPoint, along with intelligent cloud services and world-class security.
Frontline Worker Plans
Frontline workers and managers are shift-based, mobile-first workers. They are store associates, customer service representatives, nurses, doctors, factory operators, and more. Connect these employees with the tools they need to do their best work.
Integrated Service Options:

Advanced Email Protection
Comprehensive, multi-layered protection against malware.
Microsoft 365 with Advanced Email Protection
starting at £5.35 /month/user
+ taxes & fees

Backup for Microsoft 365
Protect your users with regular backups across the full Microsoft 365 tenant.
Microsoft 365 with Backup for Microsoft 365
starting at £6.95 /month/user
+ taxes & fees

Email Archiving
Tamper-proof archiving with unlimited storage.
Microsoft 365 with Email Archiving
starting at £7.39 /month/user
+ taxes & fees

Email Encryption
Protect sensitive email communications automatically.
Microsoft 365 with Email Encryption
starting at £7.39 /month/user
+ taxes & fees
Contact Us to Learn Pricing for Other Plans
Exchange Online
starting at £4.20 /month/user
+ taxes & fees




 Blair Bondar
Blair Bondar